Big Idea 5.5 Legal and Ethical Concerns and 5.6 Safe Computing Notes and Hacks
5.5 and 5.6 Big Idea Lecture Notes and Hacks
Notes
5.5 Licensing Notes
- Terms and conditions is the biggest lie in the world
- Everyone lies when they say they agree and have read the terms and conditions.
- Qualcomm has patent lawyers and makes money off of the patents that they have
- We all participate in digital rights on our phones
- Apparently we know nothing about our phones.
- Qualcomm thought that apps were not gonna go anywhere and eventually Apple pattented it.
- Music is technically digital rights, people download songs and avoid paying the artists.
5.6 Safe Computing Notes
- DO NOT TELL ANYONE YOUR PASSWORDS.
- Encrypyion, We used RSA Asynchronous Encription and 2-factor authentification when we created our blog.
- 2FA or 2-factor authentication is very prevalent all over the internet
Hacks
5.5 Licenses Hacks
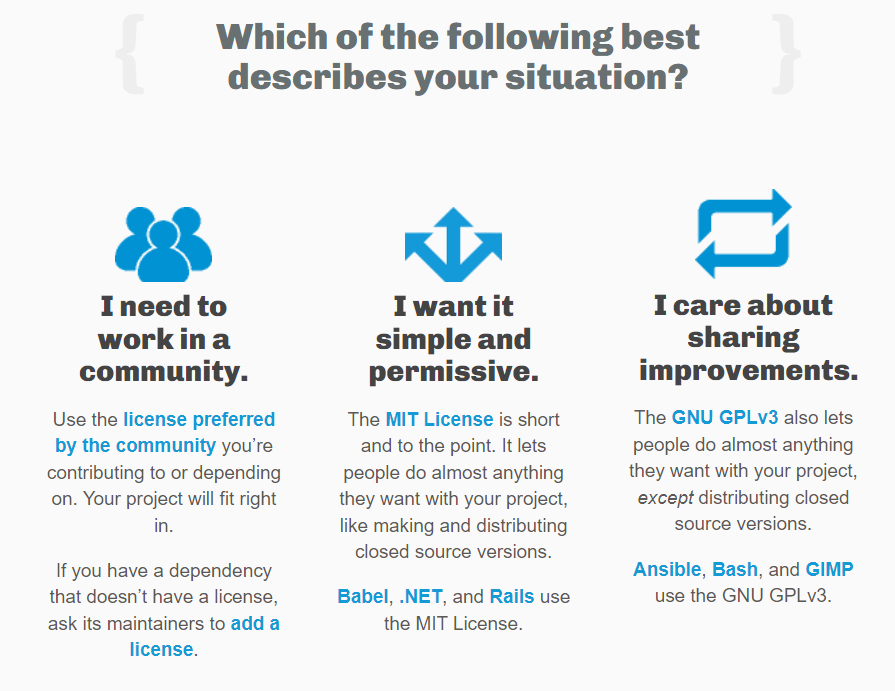
What are the differenct license types?
- There are community licences, MIT Licenses, and GNU GPLv3 Licenses.
- Community is when you contribute to the project, does not have a dependency
- MIT is short, straightforward, anyone can do almost anything with the project and make/distribute versions
- GNU lets people do anything with the project, however they cannot distribute versions of it.
-
I think for my blog I would prefer a MIT license, because I dont want people making copies of my work.
- Summarize the discussions and personal analysis on Software Licenses/Options, Digital Rights, and other Legal and Ethical thoughts from this College Board topic.
- Different licenses allow different people to do different things on and with your site/function.
- These are like patents, and big companies like Qualcomm make money off of them.
- Opensource management is completely legal for educational use, however if you want to monetise the work that you use/take from a licensed source you will have to attend to the terms of the license.
- Different licenses allow different people to do different things on and with your site/function.
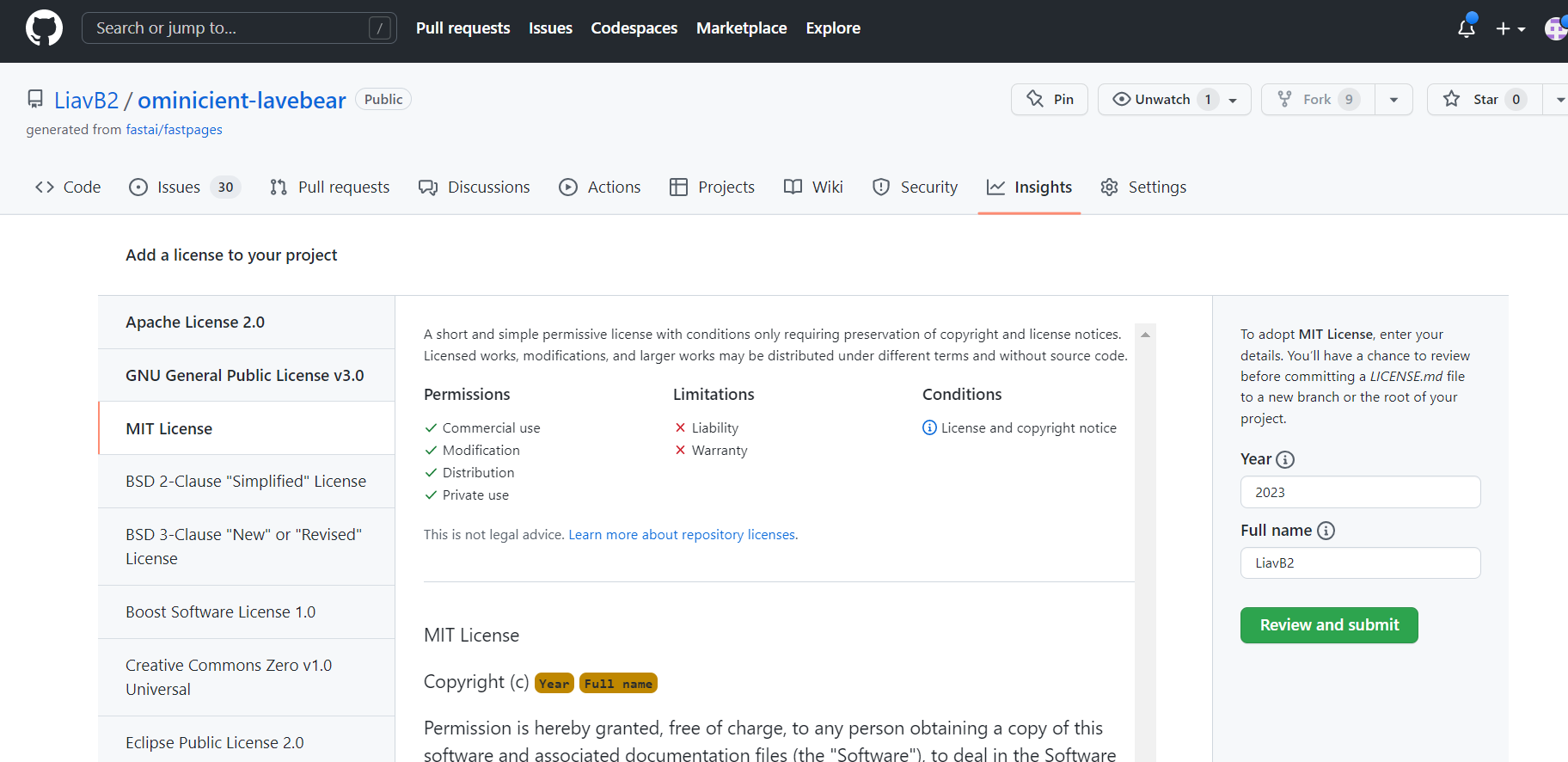
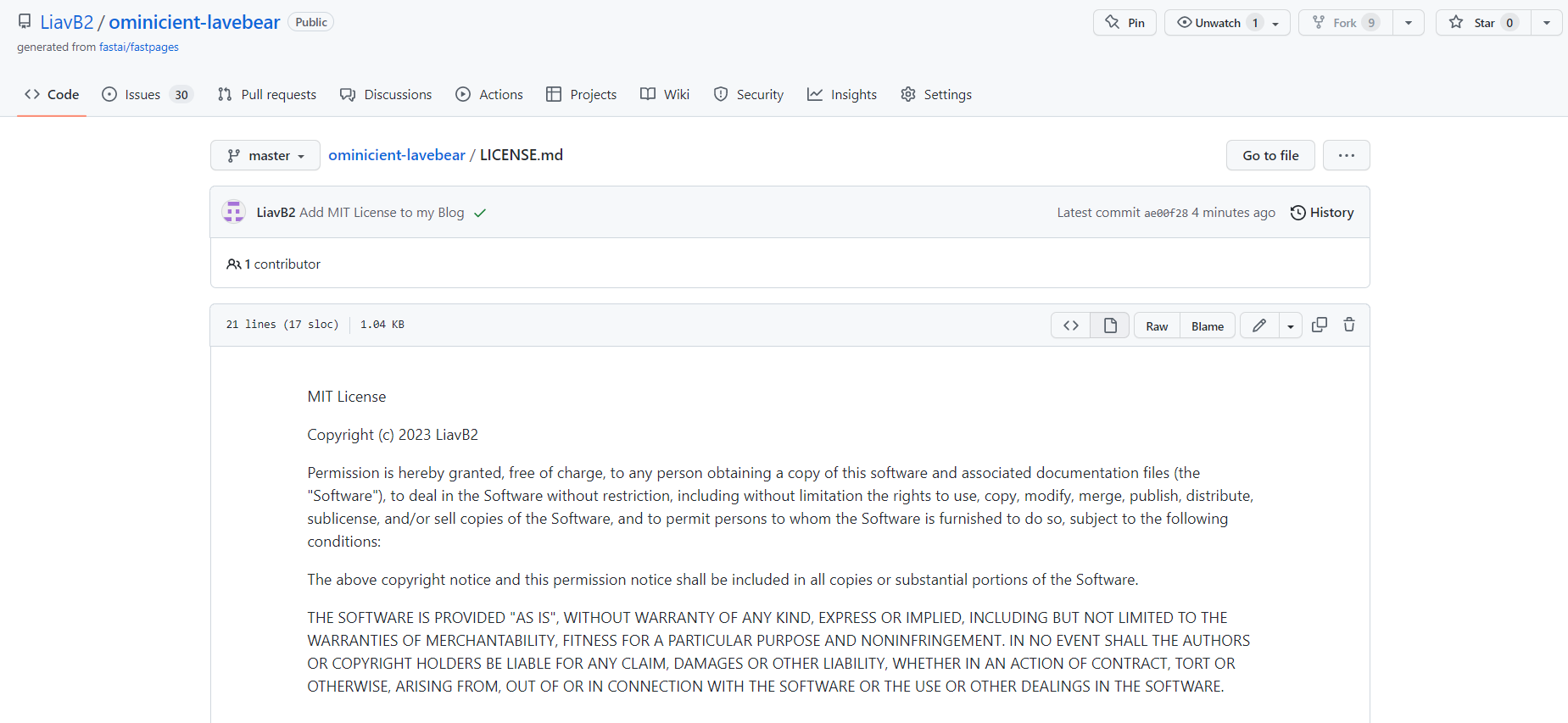
- Make a license for your personal (blog) and Team repositories for the CPT project. Be sure to have a license for both Team GitHub repositories (frontend/backend). Document license(s) you picked and why. FYI, frontend, since it is built on GitHub pages may come with a license and restrictions. Document in blog how team made license choice and process of update.
- I chose MIT for my personal blog because I don’t really care if anyone steals the work I put on it. It’s their fault for not learning and wanting to steal my work. I will only be using this site for about 4 more months anyway, so theres nothing significant that they can steal from me.
- For the group, we decided to go with an opensource GPL License, because we are ok with people using our project as inspiration and helping them wiht their own projects, so our project is public, however you cannot make copies and distribute it without infringing the terms.
5.6 Safe Computing Hacks
- Describe PII you have seen on project in CompSci Principles.
- Personal identifyable information is located all over my blog. I am ok with this because this blog is for my school project, so I need teachers and peers to be able to identify that the work on this blog is all mine.
- Therefore, all over my blog, you can see my name, my teacher, the school I go to, and even my interests.
- What are your feelings about PII and your personal exposure?
- I feel like PII is good in certain cases when you want to expose your name, or even display it for educational purposes. I think your name should be all over your work because it is important for people to know that you were the one who did your work.
- Describe good and bad passwords? What is another step that is used to assist in authentication.
- Good passwords are those that are so random, complex, and long that no person or even AI software could guess.
- Bad passwords are obvious things like your name, your dogs name, your birthday, “password”, and other common passwords that anyone can guess.
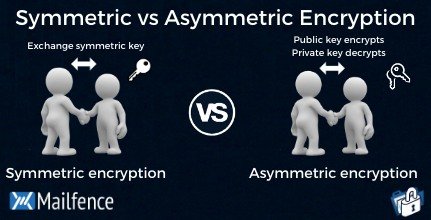
- Try to describe Symmetric and Asymmetric encryption.
- A symetric encription uses the same key to access data, and allows it so anyone who has the specific key (password) can attain access to the data.
- Asymmetric encryption uses two keys: a public and a private that are both required to attain the data.
- Provide an example of encryption we used in AWS deployment.
- In AWS deployment we used AES-256 encryption.
- the data we have on our deployed AWS sites allows it so only shared contributors to our project (via github) can pull, push, and commit changes to the main site. In doing so, we encrypted our project from public use.
- Describe a phishing scheme you have learned about the hard way. Describe some other phishing techniques.
- When I was in 7th grade I was obsessed with fortnite, and I would always see free vbuck generation schemes. I would click on them every time give them my information, and obviously be disappointed when I didn’t get my vbucks. Of course I learned about this the hard way becauseI was a naive 12 year old.
